Microsoft Threat Intelligence has revealed the discovery of a new XCSSET macOS malware variant actively targeting Xcode developers. Unlike earlier strains, this version comes with enhanced features designed to strengthen persistence and maximize data theft. It has already demonstrated capabilities to compromise browsers, hijack cryptocurrency transactions, and steal sensitive developer information.
The malware, originally known for infecting Xcode projects, continues to use its signature tactic: embedding itself into project files. Once an unsuspecting developer builds the project, the malicious code is executed. Because project files are often shared between developers working on Apple and macOS-related apps, this infection vector remains highly effective. Microsoft researchers note that this distribution model exploits the collaborative nature of software development to spread silently.
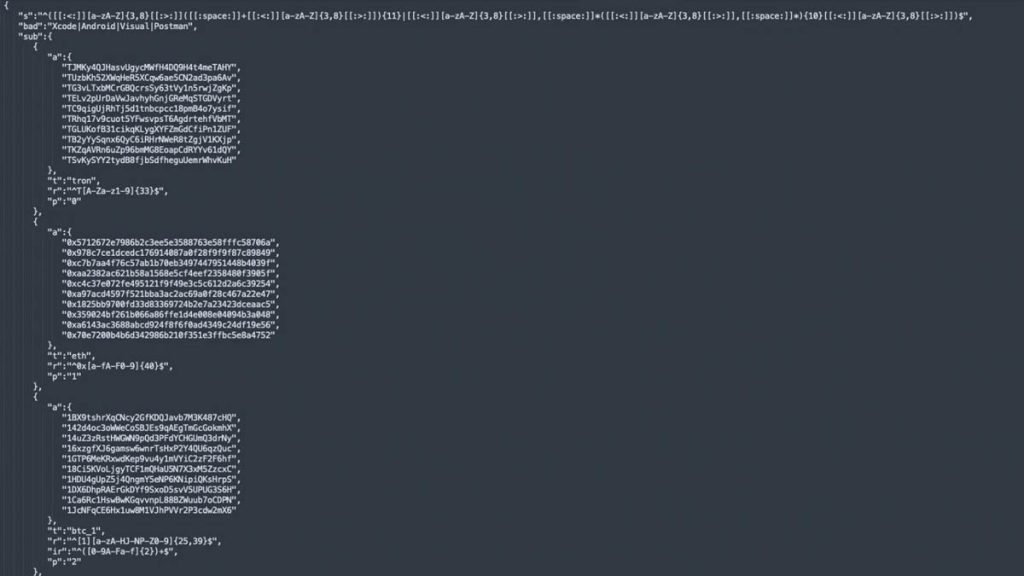
What makes this new variant particularly concerning are its upgraded data theft mechanisms. For the first time, the malware has expanded its reach to Firefox users by leveraging a modified HackBrowserData tool. This allows attackers to decrypt and extract sensitive browser data, including cookies, saved passwords, and session tokens. Alongside this, the malware now incorporates an updated clipboard hijacker. By monitoring the macOS clipboard for cryptocurrency wallet patterns, it automatically replaces a user’s intended wallet address with one controlled by the attacker, redirecting funds during transactions.
Source: Microsoft
Persistence is also a key focus for the updated strain. Researchers found that it creates LaunchDaemon entries to execute malicious payloads continuously. It even disguises its activity by creating a fake System Settings.app in temporary directories, masking its presence from users who might otherwise suspect abnormal behavior. This sophisticated evasion technique highlights the increasing effort cybercriminals are investing in macOS-targeted attacks.
At present, Microsoft has observed only limited attacks with this variant, but it has already shared its findings with Apple and GitHub to minimize further exposure. Security teams emphasize that the risk should not be underestimated, especially since previous versions of XCSSET exploited zero-day vulnerabilities in macOS to gain traction.
To mitigate risks, experts recommend that developers keep macOS and all applications updated, scrutinize Xcode projects before building, and avoid using project files from untrusted sources. As attackers focus more on cryptocurrency theft and infostealing, vigilance among developers and end users alike becomes crucial.
In conclusion, the emergence of this new XCSSET variant underscores the growing sophistication of macOS malware. While the campaign remains limited, its technical upgrades prove that attackers are adapting quickly to exploit developer ecosystems. Ensuring strict inspection practices and applying security updates remain the best defenses against these evolving threats.






