Cybersecurity experts from Crowdstrike have recently reported that hackers have learned how to inject backdoors into self-extracting WinRAR archives, effectively evading detection by antivirus software.
Understanding Self-Extracting Archives
Self-extracting (SFX) archives created with WinRAR or 7-Zip are executable files that contain archived data and embedded code to unpack it. SFX files can also be password-protected to prevent unauthorized access. Their purpose is to simplify the distribution of archived data to users who do not have a utility to extract the package.
How the Hackers Did It
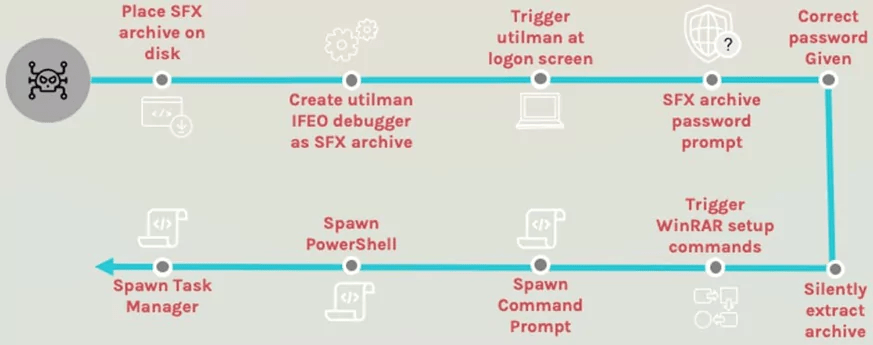
The malicious function of an SFX file is to abuse the WinRAR installation parameters to run PowerShell, the Windows command line, and Task Manager with system privileges. Crowdstrike’s experts have identified an attacker who used stolen credentials to configure the “utilman.exe” file to run a password-protected SFX archive that had been previously injected into the system.
Utilman is a special-purpose application that can be run before a user logs on to a system. Hackers often use it to bypass system authentication. The attacker configured the SFX archive in such a way that a dialogue box was not displayed during the extraction process. The hacker also added commands to run PowerShell, command line, and Task Manager.
Advanced SFX Options
WinRAR offers a set of advanced SFX options that allow you to automatically launch files, as well as overwrite existing files in the destination folder. Hackers take advantage of these features to embed malware in archives.
Be Vigilant
The researchers advise users to pay special attention to SFX archives and use appropriate software to check the contents of the archive and search for potential scripts or commands scheduled to run during extraction. Hackers continue to evolve and adapt to new security measures, and it is essential for users to remain vigilant and keep their security software updated.
Final Words
This is not the first time hackers have found a way to evade detection by antivirus software. As cybersecurity experts become aware of new tactics, hackers will adapt and develop new strategies. In the meantime, it is important for users to stay informed and take appropriate precautions to protect their systems from malware and other cyber threats.






